A compliance review request comes in. Investor due diligence, an insurance renewal, or an external audit. The team knows the policies exist. The approvals happened. Employees got a Slack message about the updates.
But the auditor wants specifics. Which version of the data handling policy was in effect last March? Who approved the expense guidelines before Q3? Can you prove employees acknowledged the security update before that incident?

And the scramble begins. Someone checks their inbox. Someone else digs through a shared drive full of files named “Final” and “Final v2” and “Final REVISED.” A compliance lead spends a week chasing timestamps from people who may or may not remember. Two weeks later, someone assembles something that resembles a record. Everyone hopes it holds up.
When I was building my previous company, we hit this exact situation during a due diligence process. We had made the decisions correctly. The policies were real too. The problem was that none of it had left a traceable record anywhere a system could confirm. We were reconstructing from memory, and that’s an uncomfortable place to be when someone external is asking the questions.
Why the trail goes cold
Someone writes policies in Google Docs, saves them to a shared drive, or drops them into a Notion page. Approvals happen over email or in a meeting. Updates go out via Slack. Nobody designs a governance record.
Nobody built shared drives, wikis, or project management tools for lifecycle tracking. Collaboration was the goal. They capture the current state of a document reasonably well. They don’t capture who approved it, in what sequence, when each person acted, or which version an employee acknowledged six months ago.
The approver chain, the change history, the acknowledgment record tied to a specific version: none of that lives in one place. It’s scattered across inboxes, Slack threads, and export files nobody can locate on short notice.
What a document audit trail needs to capture
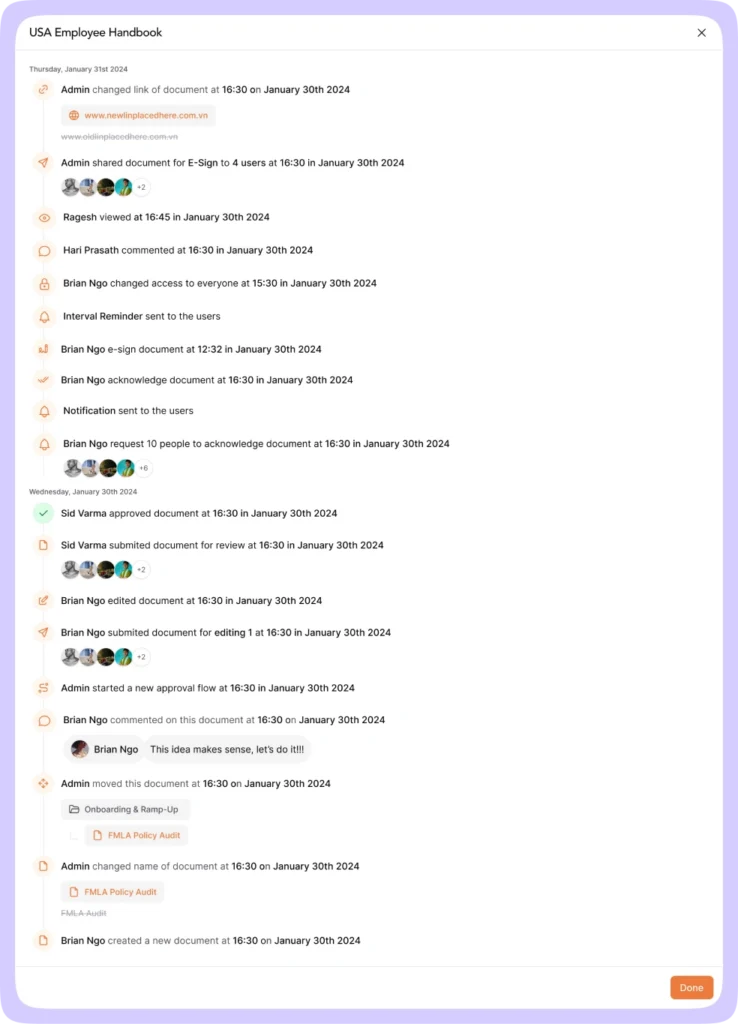
A document audit trail logs every significant action on a document chronologically, from creation onward. The word “significant” matters here. Useful audit trails don’t just log every keystroke. They capture the actions that matter for governance.
At minimum that means: who created the document and when, every edit with the editor’s name and timestamp, when the document entered review, who approved or rejected it at each step and when, when someone published it, who accessed it, and who acknowledged it against which version.
That last point is worth pausing on. An acknowledgment tied to a document is almost meaningless in a compliance context. An acknowledgment tied to a specific published version is actual evidence. If employees acknowledged your security policy in February and someone updated it in April, you need to know whether they confirmed the current version or the one that no longer reflects your practices.
Most knowledge bases and document tools don’t make that connection. They log edits. They don’t capture lifecycle. When the question comes, the gap becomes visible fast.
Version history versus version control
These terms get treated as interchangeable. They’re not, and the difference shows up at audit time.
Version history is a log of how a document changed over time. Version control is the system that governs how those changes happen and preserves a record defensible enough to hold up under external scrutiny.
Take a scenario HR managers in regulated industries know well. A leave policy is updated mid-year. Legal reviews it. The CHRO approves it. It goes live. Six months later, an employee dispute references the old policy terms, and someone asks what language was in effect on a specific date.
A list of past saves doesn’t answer that cleanly. What you need is a version snapshot: the full content of the policy as it existed at that moment, alongside who approved it and when. That’s what proper version history creates. Each time someone publishes a document or it clears an approval step, a new immutable version captures the version number, the editor’s name, a timestamp, and a change note explaining what changed and why.
You can open any past version and read it in full. You can restore it if needed, and that restoration creates a new version entry rather than overwriting the existing record. The chain of custody stays intact.
Without that, you’re asking someone to take your word for things an auditor won’t accept on faith.
Approvals that leave no record
Most teams dismiss this issue right up until a review forces it into view.
Email approvals don’t age well. People leave. Inboxes get archived. Screenshots are not lineage. When a compliance review asks who cleared the updated HIPAA policy and when, a reply-all from eight months ago retrieved from a former employee’s mailbox is not a defensible answer.
Structured approval workflows solve a specific problem: they make the approval process inseparable from the document record. Entering review locks the document from editing, moving, or deletion until the process is complete. Each approver in the defined sequence is notified when it’s their turn. Each approval or rejection appears in the log with the person’s name, role, and timestamp. The same sequence captures revisions after a rejection.
What this produces is an approver chain that lives on the document itself, not in someone’s sent folder. That’s what makes it retrievable.
There’s a secondary benefit worth knowing. Locking a document during review ensures the approver sees exactly the version that gets published. That sounds obvious until you’ve dealt with the alternative: a document quietly edited between final approval and go-live, with no system to flag it. In regulated industries, a gap between what the approver signed off on and what went live is exactly what turns a routine review into a serious problem.
The acknowledgment record that closes the loop
Policy approval is half the picture. Confirming that the right people read and acknowledged the current version is the other half. Both need to be on record. Both need to reference a specific version.
Take Rachel, compliance lead at a 200-person healthcare company. Her team updates the data handling policy following a regulatory change. It clears the approval chain. She sends a notification to the relevant teams. Four months later, an external audit asks her to demonstrate that employees confirmed receipt of the current version before the policy took effect.
Rachel has the Slack message she sent. She has no record of who clicked the link, which version was current when they did, or whether anyone followed up with the 12 people who never responded. The policy was real. The distribution happened.
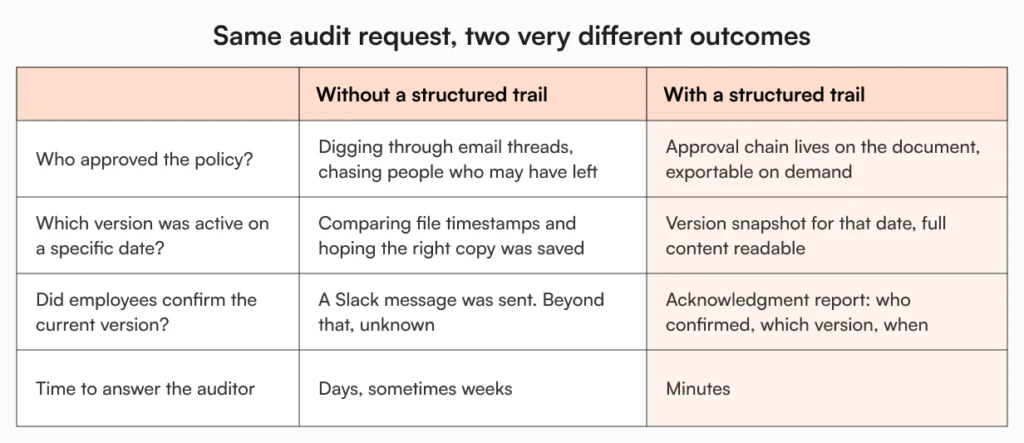
A structured acknowledgment workflow assigns the policy to a defined group with a due date. Employees confirm against the published version. Automated reminders go out to anyone who hasn’t responded. The record captures each acknowledgment with the person’s name, the document version, and a timestamp. When the audit asks, the answer is a filtered export, not a conversation with six people trying to remember.
For teams building this layer before their first serious review, startup compliance documentation covers the foundations worth putting in place early.
How AllyMatter builds the trail into the process
AllyMatter builds the document audit trail into the platform, not on top of it as a separate reporting step.
It automatically logs every significant action across a document’s lifecycle. Creation, edits, approvals at each step, publishing, folder moves – each entry records the actor, the action, the document name, and a timestamp. The log is searchable and exportable, so when a compliance review asks for the history of a specific document, the answer is a filtered export rather than a reconstruction.
Version history runs alongside this. Each time someone publishes a document or it moves through an approval step, AllyMatter creates a new immutable version with a version number, the editor’s name, a date, and a change note. Admins and document owners can open any prior version and read it in full. Restoring a previous version creates a new version entry rather than overwriting what’s already there, so the chain of custody stays intact regardless of what changes happen afterward.
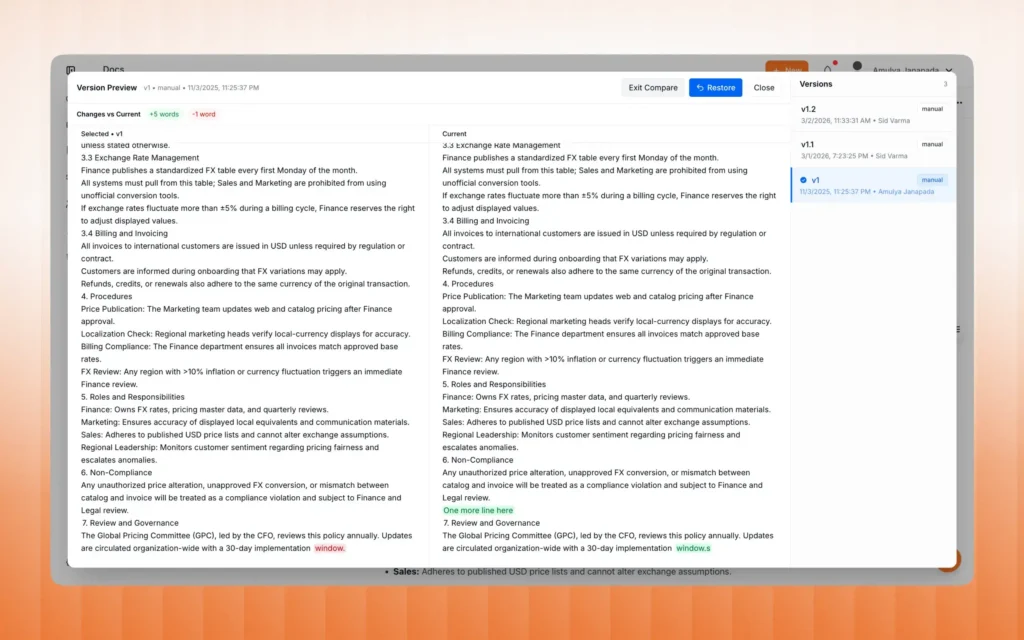
The two work together in practice. The audit trail tells you what happened and when. Version history tells you exactly what the document said at each point. For a compliance lead preparing for an external review, that combination means the record exists before the auditor asks for it.
The audit doesn’t have to be a project
The policies existed, the approvals happened, and the acknowledgments were sent. But none of it was captured in a way that surfaces on demand.
A document audit trail closes that gap by making the record a natural output of the process, not something assembled after the fact. Every action builds the record automatically. The approver clicks approve, it’s logged. The employee acknowledges, it’s logged against the version they saw. An edit creates a new version. The trail builds as the work happens.
That’s what audit readiness actually looks like for growing companies: not a folder of PDFs assembled the week before a review, but a live, searchable, exportable record that reflects everything that happened, in order, with names and timestamps attached.
Try it in the AllyMatter sandbox with pre-loaded data before you commit to anything.
Frequently asked questions
What is a document audit trail and why does it matter for growing companies?
A document audit trail is a chronological record of every significant action taken on a document across its lifecycle: who created it, who edited it and when, who approved it at each step, who accessed it, and who acknowledged it. For growing companies, it matters because compliance reviews, investor due diligence, and regulatory audits don’t ask whether your policies exist. They ask who approved them, when, and whether the right people confirmed receipt of the current version. Without a structured audit trail, answering those questions takes time you rarely have during a review.
What’s the difference between version history and version control?
Version history logs how a document changed over time. Version control governs how those changes happen and preserves a record that holds up under scrutiny. The difference matters for compliance: version history shows what changed, but version control connects those changes to the decisions behind them. For compliance purposes, you need both: the log of what changed and the structured process that gives that log credibility.
Why does it matter which version an employee acknowledged?
Because policies change. An employee who acknowledged your security policy in January may not have seen the updated version published in March. If a compliance review or dispute asks whether employees confirmed the current policy, an acknowledgment tied to the document rather than a specific version can’t answer that. Acknowledgment records need to capture the version that was live at the time of confirmation, so you can demonstrate that the right people confirmed the right content at the right time.
Why do approval emails fail as a compliance record?
Email approvals are real but fragile. People leave organizations, inboxes get archived, and a forwarded thread is not the same as a structured record. When an auditor asks for the approval history of a specific policy, an email chain from eight months ago requires locating, interpreting, and presenting in a way that an external reviewer will accept. A structured approval workflow produces a record that lives with the document itself, with names, roles, timestamps, and outcomes captured in a form that’s searchable and exportable without reconstruction.
At what point should a growing company formalize its document audit trail?
Before the first serious external review, not during it. The practical threshold is around 50 to 80 employees, when documentation starts touching multiple teams and informal processes stop being reliable. Companies that formalize early find audits less disruptive and policy disputes easier to resolve. Companies that wait tend to spend the first review assembling the record they wish they’d been keeping all along. The infrastructure takes far less effort to set up than to reconstruct under pressure.